Best Penetration Testing Companies in 2026: An Honest Comparison
Most "best penetration testing companies" lists are written by one of those companies. The rankings are circular, the criteria conveniently match whoever's hosting the post, and nobody admits where they actually fall short.
This post is different, and we'll be upfront: Red Sentry is on this list because we're a penetration testing company. We're first because we genuinely believe we're the right fit for most buyers. But we've included real tradeoffs for every vendor, including ourselves, because a CISO doing due diligence will see through anything less.
What to Look for in a Penetration Testing Company
Before getting into vendors, it's worth establishing what actually separates a useful pentest from a checkbox exercise. Use these criteria to evaluate every provider on this list, including us.
Dedicated testers, not a rotating crowd. There's a meaningful difference between a tester who understands your architecture and a random researcher encountering your environment for the first time. Tester continuity affects both the depth of findings and the quality of the audit evidence you receive.
Audit-ready documentation. For most buyers, a pentest isn't primarily about discovering unknown threats. It's about producing documentation that satisfies an auditor. SOC 2, PCI DSS, HIPAA, ISO 27001 each have specific evidence requirements. A report that doesn't map to those controls, or doesn't include an attestation letter, fails the buyer regardless of how good the testing was. See our vendor selection guide for a full breakdown of red flags to watch for.
Realistic turnaround time. The industry average for traditional manual pentests is 4 to 6 weeks from scoping to final report. If you're under a compliance deadline or closing an enterprise deal that requires a pentest certificate, that timeline is often a dealbreaker.
Transparent pricing. Most providers require a full sales cycle before sharing any numbers. Pricing opacity creates friction when you're trying to get internal budget approval, and in security, it's also a trust signal. Providers willing to publish real numbers are easier to work with and have less to hide. You can see how we approach this at our pentest cost and pricing page.
Fast scheduling. Transparent pricing means nothing if you still wait weeks to get on the calendar. The best providers can schedule your test within 1 to 2 business days of kickoff, not 2 to 3 weeks out.
Workflow integration. For development-centric teams, the ability to push findings directly into Jira rather than receiving a PDF and manually triaging is increasingly table stakes.
Human-led testing vs. automated scanning. Many providers use automation as the primary testing engine. Automated validation has real value for continuous posture monitoring, but complex business logic flaws, chained exploitation, and real adversary simulation still require experienced human testers. Confirm whether the provider assigns dedicated human testers or relies primarily on automated tooling before assuming the output satisfies your audit or threat requirements.
Verifiable certificates. After remediation, can the provider issue a publicly verifiable pentest certificate? This matters for enterprise sales cycles, partner due diligence, and customers who ask for proof rather than a PDF they can't validate.
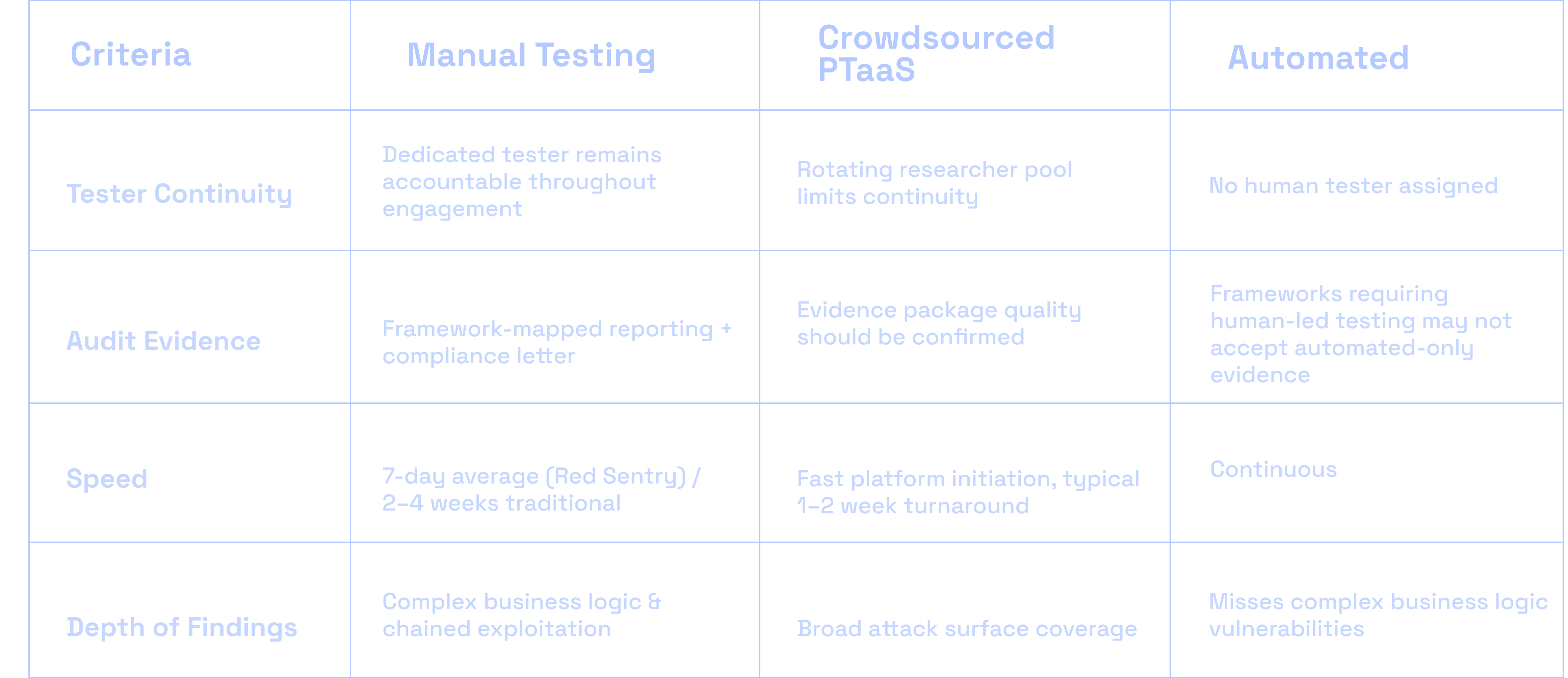
The Comparison Table
Provider | Model | Schedule to Start | Pricing | Compliance Coverage | Best Fit |
|---|---|---|---|---|---|
Red Sentry | Manual PTaaS | 1 to 2 business days | From $4,200, published | SOC 2, HIPAA, ISO 27001, PCI DSS | SaaS, healthcare, fintech, oil and gas, government, any environment where data sensitivity and audit quality both matter |
Cobalt | Crowdsourced PTaaS | 1 to 2 days (platform initiation) | Credit-based, quote required | Strong platform support | High-frequency testing programs, teams prioritizing CI/CD speed over tester continuity |
BreachLock | Hybrid PTaaS | 1 to 2 days | Published structure, quote for final | CREST-certified, strong compliance | Compliance-heavy orgs needing continuous validation |
Synack | Crowdsourced PTaaS + AI | Variable | Quote only | FedRAMP Moderate authorized | Federal agencies, large enterprise |
Bishop Fox | Manual + Cosmos platform | 2 to 4 weeks | Quote only, $25K to $75K+ | Enterprise compliance | Complex environments, Fortune 500 |
Horizon3 NodeZero | Automated | Continuous | Subscription, quote required | Control validation, some audit gaps | Continuous posture validation between manual tests |
HackerOne | Crowdsourced PTaaS + bug bounty | Variable | Quote only | Compliance support available | Broad attack surface coverage at scale |
Bugcrowd | Crowdsourced PTaaS | Variable | Quote only | Compliance support available | Scale-focused programs |
NetSPI | Manual, enterprise-focused | 2 to 4 weeks | Quote only | Deep enterprise compliance | Large enterprises, financial services |
Provider Breakdown
1. Red Sentry
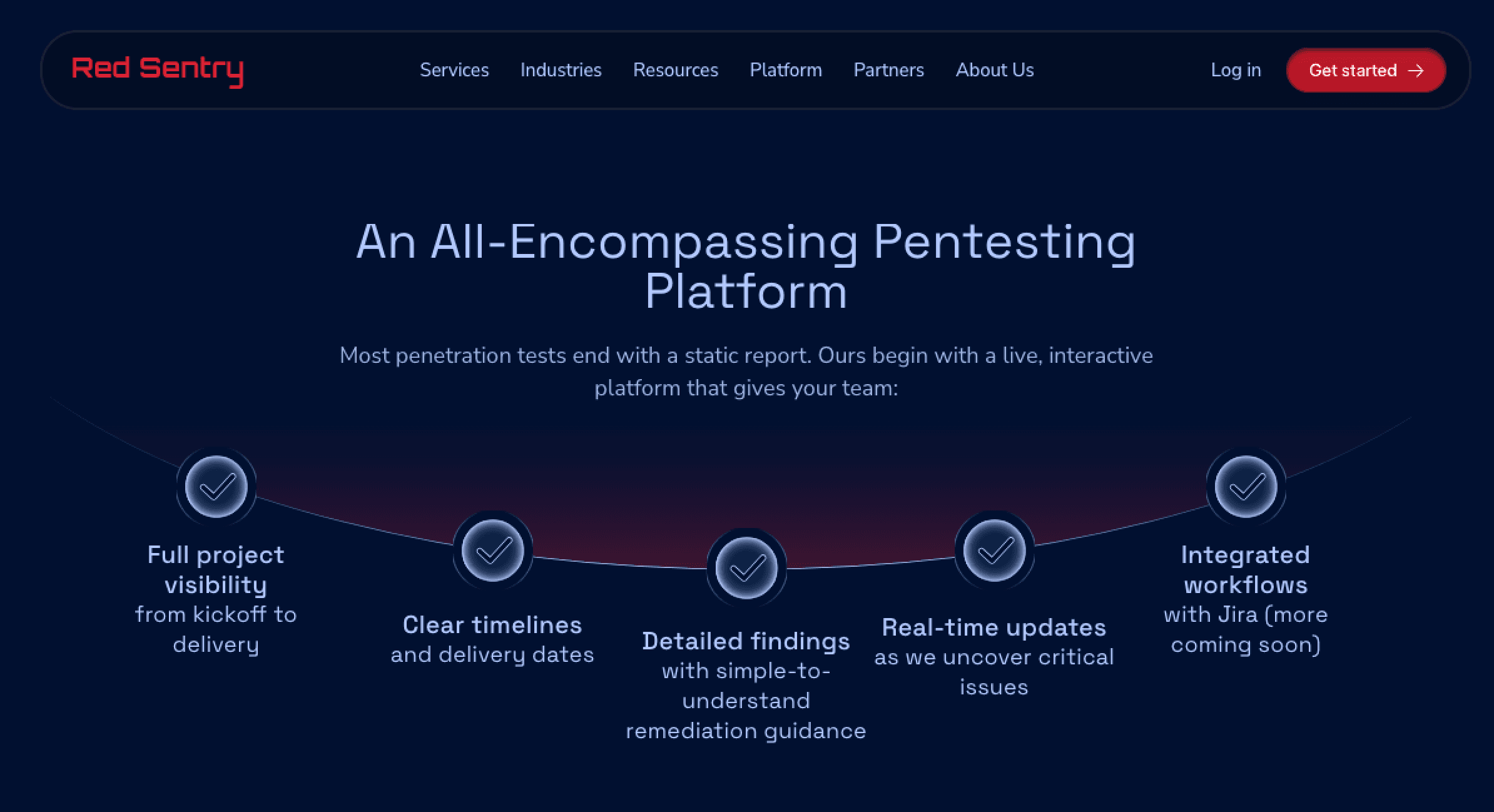
Red Sentry is a manual-first PTaaS provider built for companies that need a real pentest delivered on a timeline that works with compliance deadlines and sales cycles, not against them. The client base spans SaaS companies, healthcare and MedTech organizations, oil and gas, fintech, government contractors, and legal firms. What they have in common is sensitive data, real audit requirements, and no patience for a 6-week wait.
Testing is conducted by dedicated OSCP and OSEP-credentialed testers. Not a crowd. Not offshore by default. Engagements are led by a dedicated project manager and tester who remain accountable throughout the test lifecycle. Red Sentry's testers have published CVEs and regularly present at security conferences, which reflects the depth of capability behind compliance-focused engagements that are easy to dismiss as routine work.
Scheduling is open within 1 to 2 business days of kickoff. Average time from start to final report runs around 7 days, substantially faster than the 4 to 6 week industry standard. Every engagement includes a dedicated project manager, real-time findings through the platform, Jira integration, a compliance letter, and a free remediation retest. Pricing starts at $4,200 and is published on the website, not gated behind a sales call.
Every completed engagement includes a publicly verifiable pentest certificate, something most providers don't offer, which matters when enterprise prospects or compliance auditors want proof rather than a PDF they can't validate.
Coverage spans SOC 2, HIPAA, ISO 27001, PCI DSS, and more. Red Sentry has purpose-built testing programs for healthcare, fintech, SaaS, legal, education, and government, among others.
Strengths: Scheduling within 1 to 2 business days, 7-day average turnaround, OSCP/OSEP testers with published CVEs and conference credentials, audit-ready documentation, transparent published pricing starting at $4,200, verifiable pentest certificates, Jira integration, purpose-built programs for regulated industries.
Where we're not the best fit: If you're a Fortune 500 running a mature continuous program that requires hundreds of concurrent researcher-hours across dozens of assets simultaneously, a larger crowdsourced platform will give you a scale we don't offer. For everything else, including red team engagements, we're worth a conversation.
Best for: SaaS companies preparing for SOC 2, healthcare and MedTech organizations navigating HIPAA, oil and gas and energy companies with operational technology exposure, government contractors, fintech, and any organization where the standard 4 to 6 week timeline creates a real business problem.
2. Cobalt
Cobalt pioneered the modern PTaaS model and remains one of the most recognized names in the space. The platform connects clients to a vetted community of 450+ pentesters via a credit-based model (one credit = eight hours of testing). Cobalt markets test initiation within 24 hours, though this refers to platform kickoff rather than a dedicated tester beginning work on your environment. Full engagement turnaround typically runs 1 to 2 weeks.
Pricing requires a custom quote. The annual credit model can become expensive for organizations running frequent tests across large scopes.
Strengths: Fast initiation, strong Jira and CI/CD integration, flexible credit-based model, real-time collaboration, large vetted tester community.
Limitations: Rotating researcher pool limits continuity across engagements. Buyers with strict audit requirements should confirm evidence package quality before assuming it satisfies their specific framework.
Best for: SaaS and fintech companies with agile release cycles that need testing integrated into development workflows. Less suited for situations requiring a tester who builds deep familiarity with your environment over time.
3. BreachLock
BreachLock runs a hybrid model combining manual testing by in-house CREST-certified testers with automated scanning on a unified platform. Gartner has recognized them as a sample vendor for PTaaS continuously since 2021 more third-party analyst credibility than most mid-market providers carry. Tests can be scheduled within 1 to 2 business days, and they publish a pricing structure rather than requiring a full sales cycle to get numbers.
Their January 2026 launch of an agentic AI layer extends automated testing to web application attack surfaces, which positions them well for continuous validation use cases alongside their manual work.
Strengths: CREST certification, consistent Gartner recognition, hybrid automated/manual approach, published pricing structure, strong compliance documentation.
Limitations: Teams that require extreme manual testing depth sophisticated adversary simulation, complex chained exploitation may find the automation-forward hybrid model less thorough than a pure manual provider.
Best for: Compliance-heavy organizations in healthcare, financial services, and regulated industries that want a recognized credential on the attestation and need regular ongoing testing rather than one-off engagements.
4. Synack
Synack sits at the premium end of crowdsourced testing. The Synack Red Team is a curated, highly vetted researcher community (not an open platform), and their SARA AI layer steers human testers toward higher-impact targets. They're the only crowdsourced pentest provider authorized at FedRAMP Moderate, which makes them the default choice for federal agencies and contractors.
Continuous testing options (Synack365) allow organizations to move beyond point-in-time assessments toward ongoing coverage. Pricing is premium and requires a full sales engagement to understand.
Strengths: Elite researcher vetting, AI-assisted targeting, FedRAMP authorization, continuous testing options, global 24/7 researcher coverage.
Limitations: The platform fees, credit structure, and engagement overhead are more than most single-engagement compliance tests warrant. Not designed for mid-market buyers who need a straightforward audit deliverable on a predictable budget.
Best for: Federal agencies, defense contractors, large enterprises with continuously-changing attack surfaces that benefit from ongoing coverage rather than annual point-in-time tests.
5. Bishop Fox
Bishop Fox is the benchmark for deep, expert-led manual pentesting. Their team publishes CVEs, speaks at Black Hat, and builds widely used offensive security tools. When the question is "can someone find what automated tools and average testers miss," Bishop Fox is the answer, and the pricing reflects it.
The Cosmos platform enables continuous attack surface testing for clients who want always-on coverage. Standard engagements run 2 to 4 weeks. Budget $25,000 to $75,000+ for enterprise engagements depending on scope.
Strengths: Unmatched technical depth, research-driven team, Cosmos continuous platform, exceptional for IoT, embedded systems, and custom attack surfaces.
Limitations: Bishop Fox prioritizes depth over rapid scheduling. Engagements run 2 to 4 weeks, and the price point is out of range for most mid-market buyers who need equivalent audit evidence at a fraction of the cost.
Best for: Large enterprises and Fortune 500 companies with complex environments where standard methodology isn't sufficient, and organizations that view security testing as a strategic program rather than a compliance exercise.
6. Horizon3 NodeZero
NodeZero takes a fundamentally different approach: fully autonomous pentesting that runs continuously without human testers. The platform discovers attack paths and simulates exploitation without agents or credentials, producing a risk-prioritized remediation roadmap. For organizations that want to verify their patching is actually closing gaps, not just that patches were applied, the continuous validation model has real value.
Strengths: Continuous posture validation, agentless deployment, fast production-safe testing, useful for validate/fix/verify loops.
Limitations: Automated testing is genuinely useful for continuous control validation and remediation verification, but it misses complex business logic vulnerabilities and creative exploitation chains that experienced human testers find. Compliance frameworks that explicitly require human-led testing (PCI DSS 11.3 being the clearest example) won't accept automated-only evidence. NodeZero works best as a complement to manual testing, not a replacement for it.
Best for: Security teams wanting continuous validation between annual manual tests. Should be paired with a manual provider not used as a replacement for compliance-driven engagements.
7. HackerOne & Bugcrowd
Both started as bug bounty platforms and expanded into structured PTaaS. Their core strength is researcher scale HackerOne has one of the largest vetted researcher communities globally, and Bugcrowd has grown rapidly in structured PTaaS engagements.
The crowdsourced model tradeoffs apply to both: variable tester continuity, pricing that requires a sales engagement to understand, and compliance evidence quality that buyers should validate carefully before assuming it satisfies their specific framework. Both platforms have improved compliance reporting, but the evidence packages are worth scrutinizing before signing.
Strengths: Massive researcher pools, flexible engagement models, strong brand recognition, continuous testing options.
Limitations: Tester continuity, pricing predictability, and compliance evidence quality all vary. Best suited for organizations that can manage the engagement complexity that comes with scale.
Best for: Large organizations with broad attack surfaces who want diverse researcher perspectives. Less suited for mid-market buyers who need a predictable, auditor-accepted deliverable.
8. NetSPI
NetSPI is the largest purely manual pentesting firm in the US, with 300+ in-house experts serving major financial institutions and Fortune 500 companies. High-touch, consultative engagements with deep compliance methodology. Their Resolve platform tracks findings over time.
Strengths: Large dedicated in-house team, deep financial services and healthcare compliance pedigree, consultative model.
Limitations: Not competing on speed or price. Engagements run 2 to 4 weeks and are priced for enterprise budgets.
Best for: Large enterprises and heavily regulated organizations particularly financial services and healthcare that need a strategic security testing partner and have the budget for it.
How to Choose: A Decision Framework
The right provider comes down to three variables: your compliance driver, your timeline, and your budget.
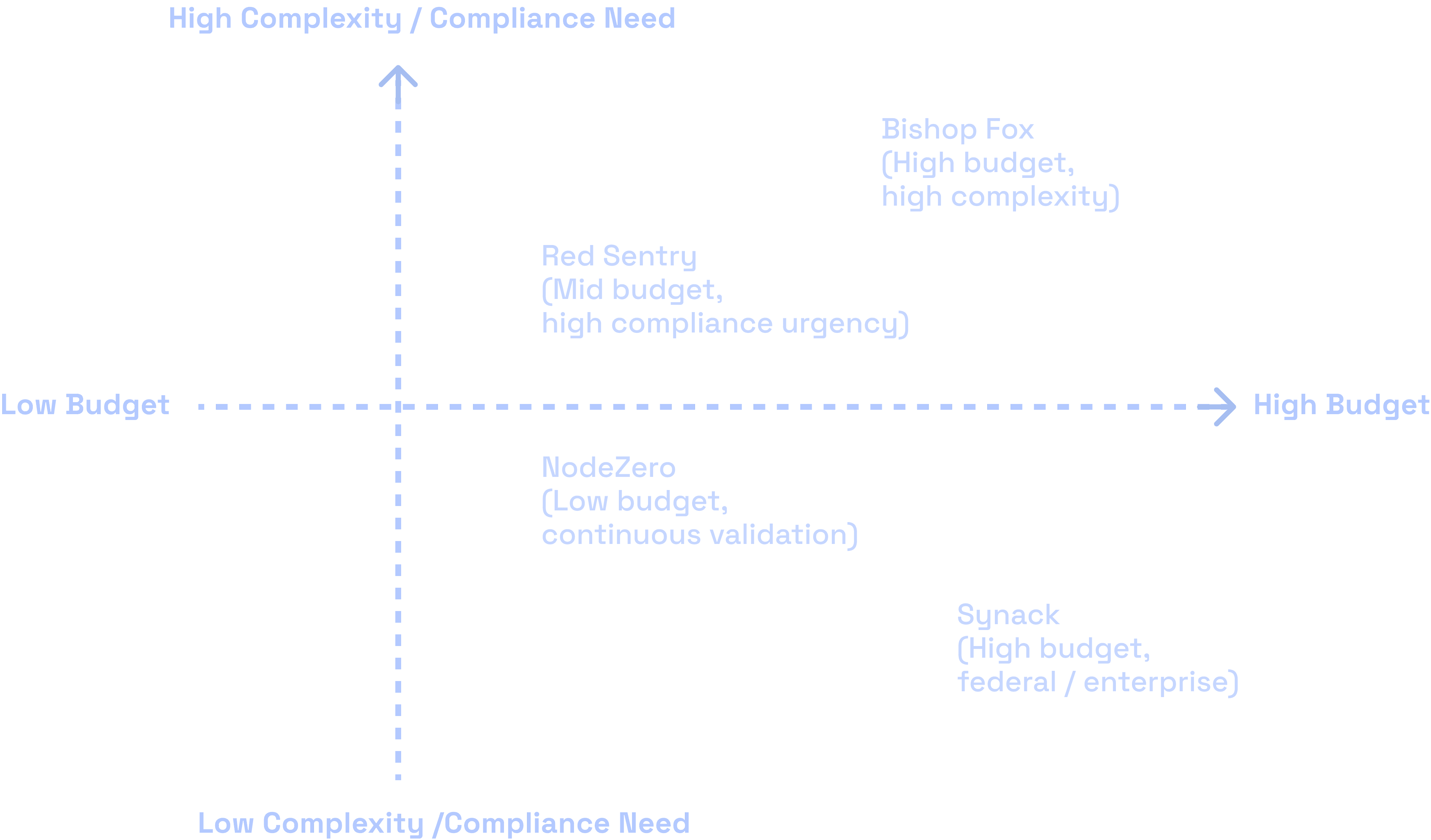
Under a compliance deadline? Your primary criteria should be turnaround time, audit-ready reporting, and tester credentials that auditors recognize. Automated tools can support continuous validation but typically don't satisfy compliance frameworks that require human-led testing. Crowdsourced models need careful vetting for evidence quality. Manual providers with fast turnaround and compliance-specific reporting will clear the most audits without friction. Our vendor selection guide walks through the specific questions to ask and red flags to watch for.
Complex environment, mature security posture? If you want to know what a sophisticated attacker would actually find, not just what passes an audit, look for a provider whose testers publish CVEs, speak at security conferences, and have deep specialization in your specific environment type. That level of expertise commands a premium and a longer timeline.
Running a continuous program? If you're integrating testing into your development process with frequent cadences, the PTaaS model (Cobalt, BreachLock, Red Sentry) or automated validation (NodeZero) makes more economic sense than annual bespoke engagements.
Not sure what scope you actually need? Our pentest cost guide breaks down how pricing works across different environments, compliance requirements, and engagement types, with no sales call required to get numbers.
Frequently Asked Questions
What is the fastest penetration testing company?
For manual pentests, Red Sentry averages around 7 days from kickoff to final report, with scheduling available within 1 to 2 business days. Crowdsourced platforms like Cobalt market fast platform initiation, though full engagement turnaround typically runs 1 to 2 weeks. The industry standard for traditional consultancies is 4 to 6 weeks.
Which pentest company is best for SOC 2 compliance?
Any provider offering dedicated manual testers and explicit SOC 2 control mapping will work. Confirm the deliverable includes the specific evidence format your auditor expects before engaging not all compliance letters are created equal. Red Sentry, BreachLock, and Cobalt all support SOC 2 engagements.
What's the difference between PTaaS and traditional penetration testing?
Traditional pentesting is a scoped, time-boxed manual engagement delivered as a final PDF report. PTaaS adds a platform layer: real-time findings, continuous retesting, SDLC integrations, and ongoing access to your vulnerability data. PTaaS models typically produce more actionable output for development-centric teams.
Is crowdsourced pentesting as good as dedicated manual testing?
For broad attack surface coverage and diverse researcher perspectives, crowdsourced testing has real advantages. For audit evidence quality, tester continuity, and deep understanding of your specific architecture, dedicated manual testers win. The two models serve different needs use the compliance driver and environment complexity to decide which fits.
What certifications should a pentest provider have?
OSCP (Offensive Security Certified Professional) is the most widely recognized hands-on credential. It requires real-world exploitation under time pressure, not just a multiple-choice exam. OSEP signals advanced capability beyond the standard. CREST certifies the firm rather than individuals and carries weight for PCI DSS and international frameworks. Be skeptical of providers whose testers hold only theory-based certifications. See our vendor guide for more on what credentials actually mean in practice.
How much does a penetration test cost?
A basic web application pentest from a mid-market PTaaS provider typically starts around $4,200 to $15,000. Enterprise engagements with Bishop Fox or NetSPI can run $25,000 to $75,000+. Annual PTaaS platforms like Cobalt or Synack typically run $20,000 to $100,000+ depending on testing frequency and scope. For a full breakdown of what drives pentest pricing, see our pentest cost guide.
Does penetration testing methodology matter for compliance?
Yes. Different frameworks require different testing approaches and evidence. NIST SP 800-115, PTES, and OWASP are the most commonly referenced methodologies in compliance contexts. See our testing methodologies page for how Red Sentry's approach maps to major compliance frameworks.
How does penetration testing differ by industry?
Significantly. Healthcare testing has to account for HIPAA, ePHI exposure, and often connected medical devices. Fintech requires PCI DSS expertise and understanding of payment APIs. SaaS companies have different risk profiles than law firms or manufacturers. Generic testing that doesn't account for your sector's specific threat landscape and regulatory requirements produces weaker findings and weaker audit evidence. See our industry-specific testing programs for how Red Sentry approaches different verticals.
This comparison draws on publicly available vendor information, G2 and TrustRadius reviews, third-party analyst reports, and Red Sentry's direct market experience. Pricing ranges are estimates based on available market data and should be verified directly with vendors.
Best Penetration Testing Companies in 2026 | Red Sentry
