Blogs
Cybersecurity Blog
Stay ahead with insights from Red Sentry’s team, covering penetration testing, compliance, and offensive security trends.

PENTESTING TEAM, TOOLS AND TECHNIQUES
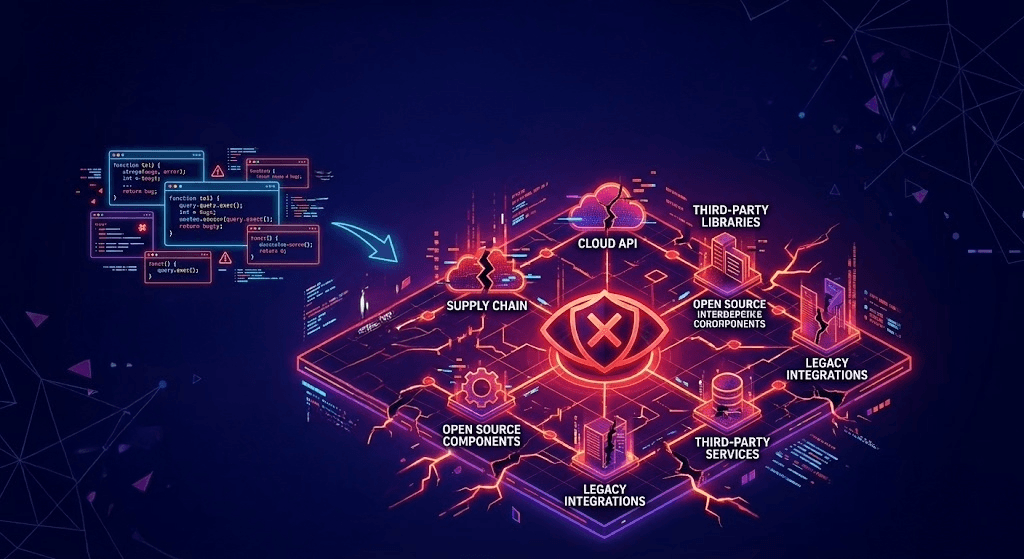
The 2025 OWASP Shift: From "Bad Code" to "Broken Ecosystems"
Modern web security has shifted from fixing isolated coding flaws to protecting interconnected ecosystems, requiring organizations to secure complex APIs, CI/CD pipelines, and third-party dependencies through continuous, holistic penetration testing.


INDUSTRY
The Attorney-Client Privilege Portal: Why Encryption isn't Security
Encryption only protects data in transit, not its integrity. Without validation, malicious files uploaded via client portals can bypass security, allowing hackers to compromise legal servers and exfiltrate confidential data.


PENTESTING TEAM, TOOLS AND TECHNIQUES
Identity is the New Perimeter: Bypassing MFA in Web Apps
Cybersecurity has shifted from firewalls to identity-based perimeters. However, attackers bypass traditional MFA through session hijacking, token theft, and fatigue tactics. Organizations must adopt phishing-resistant authentication to secure cloud-based applications.


PENTESTING TEAM, TOOLS AND TECHNIQUES
Securing the "Prompt": Defending Web Apps with Integrated LLMs
Integrating LLMs into web apps creates "Prompt Injection" risks, where malicious prose tricks models into bypassing security. Organizations must use privilege minimization and rigorous filtering to prevent AI from becoming a "confused deputy."


PARTNERSHIP ANNOUNCEMENT
SOC 2 Shouldn’t Be a Fire Drill - It Should Be How You Already Operate
SOC 2 should be a continuous operational standard, not an annual scramble. By integrating Rippling’s automated enforcement with Red Sentry’s independent validation, companies achieve genuine security instead of just compliance


PENTESTING TEAM, TOOLS AND TECHNIQUES
AI SOC: Can It Be Trusted?
The agentic AI SOC offers efficient, continuous compliance through autonomous evidence gathering. However, potential hallucinations and lack of context mean it should serve as a co-pilot, requiring human oversight for validation.