Recent reporting around the Rockstar Games breach highlights a pattern that’s becoming more common and more dangerous.
This wasn’t a direct compromise of Rockstar’s infrastructure. Attackers targeted a third-party SaaS provider, extracted authentication tokens, and used those to access Rockstar’s Snowflake environment.
That distinction matters.
This wasn’t a failure of perimeter defenses or an exposed service. It was a failure in how trust is extended to third-party systems, and how that trust is monitored once established.
Most organizations treat vendor access as a necessary risk. A SaaS platform gets integrated, credentials or tokens are issued, and access is granted so the service can function.
What often gets overlooked is that this trust doesn’t stop at the integration point.
If a third-party system has access to your internal data or services, it effectively becomes part of your environment from an attacker’s perspective. Compromising that vendor doesn’t just give access to their systems, it can provide a direct path into yours.
In this case, attackers didn’t need to break in. They used a trusted relationship to walk in.
How This Actually Happens
Unlike user credentials, service tokens and API keys are rarely treated with the same level of scrutiny. They are often long-lived, broadly scoped, and not tied to MFA or interactive login. Once issued, they are rarely monitored closely.
Once an attacker obtains a valid token, there is no exploitation required. They authenticate as a trusted service and continue operating as expected.
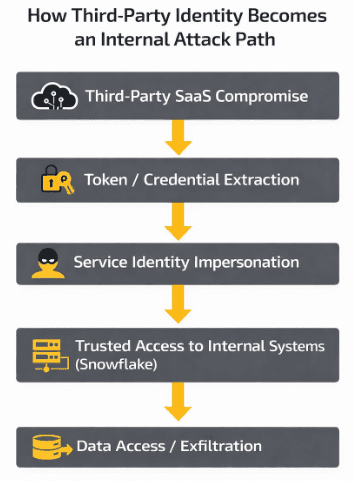
From there, the path is straightforward:
Extract tokens from the compromised vendor
Impersonate the service identity
Access internal systems using trusted connections
Move directly to data
The diagram below shows how quickly that trust relationship becomes an attack path.
Why This Works
What makes this type of breach effective is how clean the attack path is.
There is no noisy exploitation chain. No obvious lateral movement in the traditional sense. Each step appears valid in isolation.
Traffic from a known SaaS provider is expected. Authentication using valid tokens is expected. Access to internal systems is expected.
That’s what makes this difficult to detect.
Most security programs are still built around clear boundaries, external vs internal, trusted vs untrusted. Third-party integrations blur those lines to the point where those distinctions stop being useful.
This isn’t about whether access is valid. It’s about whether the behavior behind that access still makes sense.
The Real Risk
These incidents tend to come down to the same underlying issues.
Third-party access is over-scoped and rarely revisited. Service identities are not monitored the same way user accounts are. There is little segmentation between external integrations and sensitive systems.
Individually, these don’t always stand out as critical. Combined, they create a path attackers can move through without resistance.
If a vendor has access to your systems, their compromise becomes your compromise.
At that point, the distinction between internal and external stops mattering.
The Takeaway
This isn’t just a third-party risk problem. It’s a visibility problem.
Security teams have to shift focus from where access originates to how that access behaves once it exists.
Because in cases like this, the attacker isn’t forcing their way in.
They’re operating inside a system that already trusts them.
When Your Vendor Becomes Your Entry Point

When Your Vendor Becomes Your Entry Point
Apr 14, 2026
Mike Shelton
Head of Pentesting