What Happens After Initial Access: Why Internal Network Testing Matters
Recent incidents have highlighted a pattern we see over and over again.
Initial access usually isn’t the hardest part.
Whether it’s a compromised credential, a phishing email, or an exposed service, attackers don’t need much to get a foothold. What actually determines the impact of an incident is what happens next.
And in most cases, that’s where things start to break down.
The Blind Spot Isn’t the Perimeter
Most organizations spend a lot of time securing external access points. Firewalls are hardened, endpoints are monitored, and external testing is done regularly.
But once an attacker is inside the network, the assumptions change.
Internal systems tend to trust each other. Access is often broader than it needs to be. Monitoring is focused on external threats, not authenticated activity. So someone with even limited access can start exploring the environment without much resistance.
This is where things shift.
What Attackers Do After They Get In
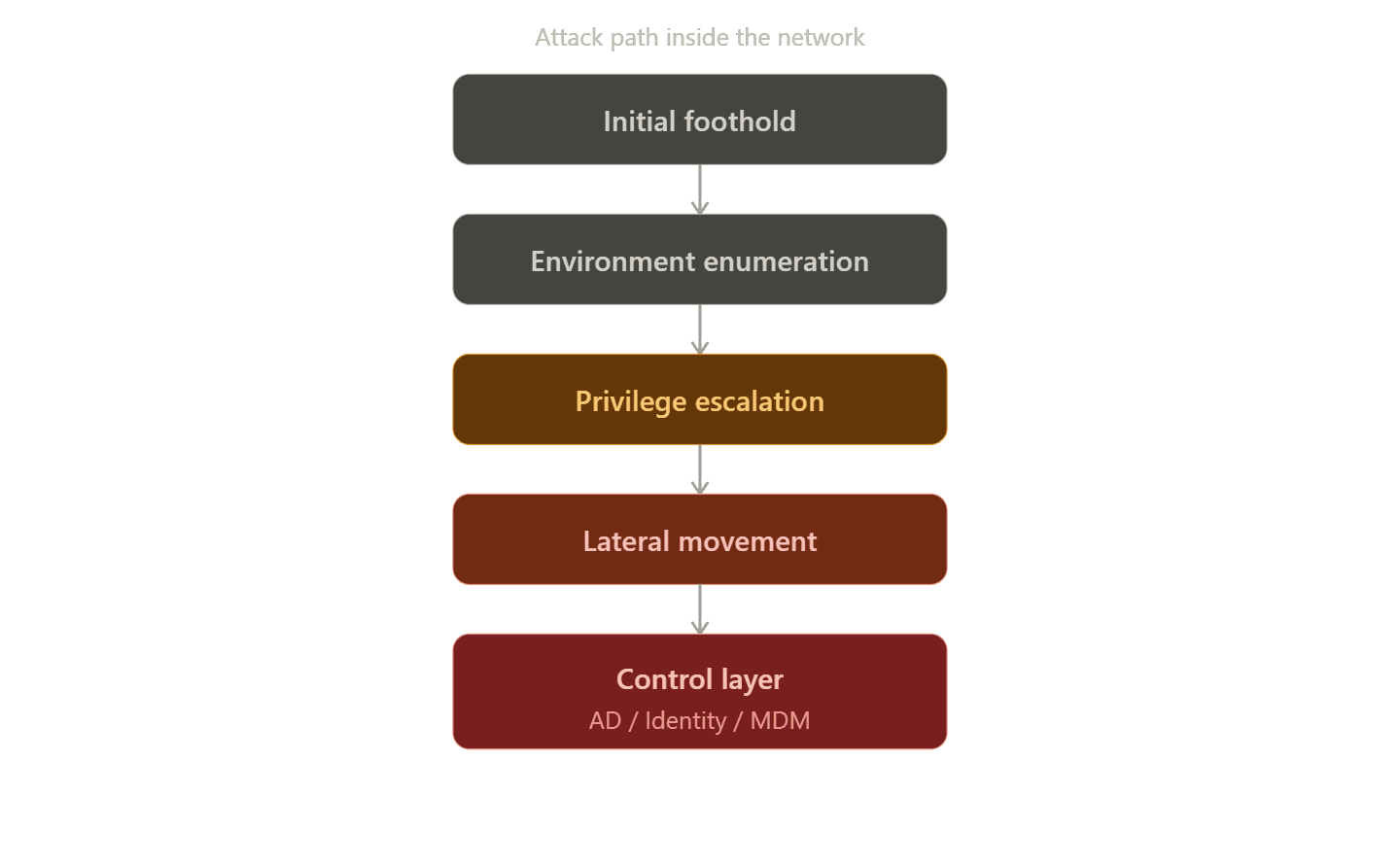
Once inside, attackers don’t move randomly. There’s usually a pattern to how they approach an environment.
They start by figuring out what’s there, what systems exist, how they communicate, and which accounts have access to what. From there, the focus is on increasing access. That might be through weak permissions, reused credentials, or configurations that were never meant to be exposed internally.
In internal tests, this is exactly where environments tend to break down. It’s rarely one major issue. It’s a series of smaller ones that weren’t expected to interact.
As privileges increase, movement becomes easier. Systems that were out of reach start to become accessible. Trust relationships between services and users allow access to expand without needing to exploit every system directly.
At a certain point, the objective is to reach a control layer, something like Active Directory, identity infrastructure, or a centralized management system. Once that happens, the attacker doesn’t need to move laterally anymore.
Control is already established.
Why This Progression Often Goes Unnoticed
The challenge isn’t just that this activity is happening.
It’s that most of it looks legitimate.
Authenticated access doesn’t always raise alerts. Administrative actions can blend in with normal operations. Movement between systems often follows expected communication paths.
From the outside, it can look like a sudden, large-scale incident.
In reality, it’s usually a gradual progression that wasn’t interrupted.
Where Environments Actually Break Down
In most cases, this kind of movement isn’t caused by a single critical vulnerability.
It comes down to how access is structured across the environment.
Permissions are broader than intended. Credentials get reused across systems. Segmentation is inconsistent or missing altogether. And internal activity doesn’t get the same level of scrutiny as external traffic.
Individually, these issues often don’t raise concern.
Combined, they create a path.
Where Internal Network Testing Fits
Internal network testing is meant to surface those paths.
It focuses on what happens after initial access, not just whether access is possible in the first place.
Instead of looking at vulnerabilities in isolation, it shows how they actually play out together. How far an attacker could move. What systems become reachable. Where privilege escalation becomes possible.
That’s the difference.
It’s not just about finding issues. It’s about understanding how access behaves in practice.
Breaking the Attack Path
Like any intrusion, there are multiple points where this progression can be interrupted.
Reducing initial access limits footholds. Tight control over privileges makes escalation harder. Segmentation and identity controls restrict movement. Monitoring internal activity increases the chance of catching something before it turns into full control.
No single control solves it.
What matters is how they work together.
The Real Takeaway
Most organizations don’t fail because someone got in.
They fail because of what happens after.
Initial access isn’t usually the hardest part. The real risk is how far that access can go once it’s inside.
Understanding that progression is what makes internal testing valuable. It shifts the focus from individual vulnerabilities to how access actually works across the environment.
Because the real risk isn’t just entry.
It’s what happens next.
What Happens After Initial Access: Why Internal Network Testing Matters

What Happens After Initial Access: Why Internal Network Testing Matters
Apr 13, 2026
Mike Shelton
Head of Pentesting