Anatomy of a Meltdown: What the Handala Attack on Stryker Teaches Us About Privilege Escalation
Last week, reports emerged of a destructive cyberattack attributed to the Iranian-linked hacktivist group “Handala” targeting Stryker. Public reporting indicates widespread operational disruption across multiple regions, along with large-scale device wiping and data exfiltration.
Headlines are naturally focusing on the geopolitical motivations, specifically the retaliation for recent military strikes on Iran, and the alarming use of wiper malware.
Instead of focusing on headlines, the more useful question is how an attack like this actually unfolds inside an environment.
Most Attacks Begin With Limited Access
We often hear the term "advanced persistent threat" and assume attackers start with full control or complex zero-day exploits right out of the gate.
They typically gain a foothold through something relatively ordinary that regular external network penetration testing is designed to catch. Threat intelligence on Handala’s historical tactics shows they rely heavily on:
Exposed services and commercial VPN nodes
Weak, compromised, or brute-forced credentials
Default hostnames and misconfigurations
Vulnerabilities in internet-facing systems
At this initial stage, the attacker’s access is usually limited. The compromised perimeter system might even lack valuable data. The real danger is what the attacker can reach from that initial beachhead.
Privilege Escalation Changes Everything
Privilege escalation is the exact point where a nuisance intrusion turns into a catastrophic breach.
Once attackers move from limited access to administrative control, their capabilities expand exponentially. Early forensic reports on the Stryker attack indicate the threat actors bypassed deploying malware immediately. They first escalated privileges to obtain Domain Administrator credentials.
With those keys to the kingdom, Handala weaponized the company's own IT infrastructure. By abusing native, trusted deployment tools like Microsoft Intune and Group Policy Objects, the attackers reportedly pushed operating system reset commands and destructive wiper scripts.
This allowed them to impact hundreds of thousands of corporate laptops, mobile phones, and servers worldwide.
Privilege escalation weaknesses are the common denominator in major cyber incidents for a reason. Elevated privileges allow attackers to disable monitoring tools, modify configurations, and push destructive payloads across the environment.
Attackers Build Paths Through Environments
These incidents rarely succeed because of a single vulnerability. Attackers build attack paths by chaining together multiple smaller weaknesses. Based on reporting from Kim Zetter at Zetter Zero Day, the Handala incident follows a typical 5-phase escalation pattern seen in many major breaches.
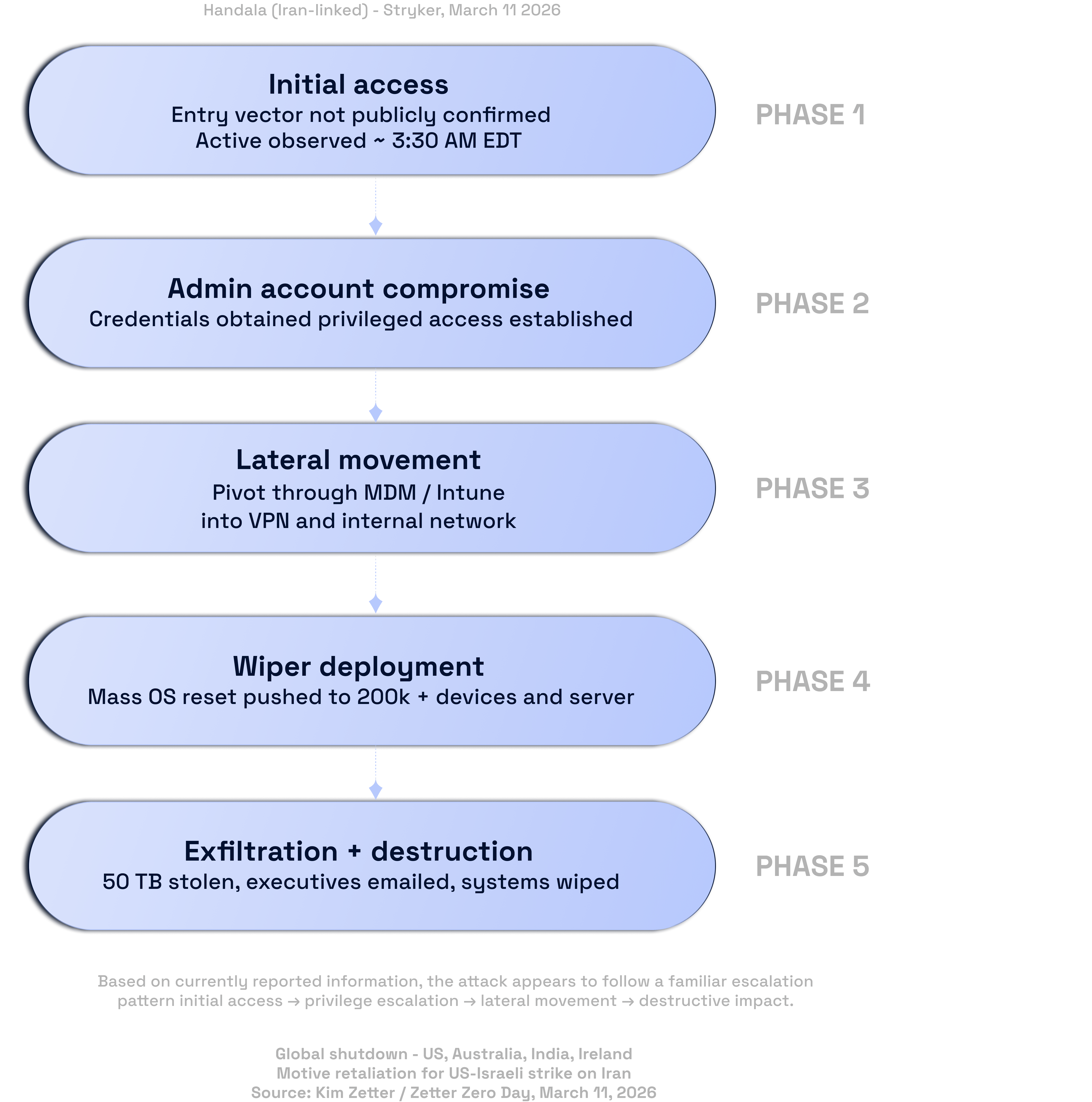
Handala (Iran-linked) attack on Stryker, March 2026. Phase breakdown showing initial access to destructive impact.
The sequence we are seeing unfold looks exactly like this:
Phase 1: Initial Access: The entry vector has not been publicly confirmed, but activity was observed around 3:30 AM EDT.
Phase 2: Admin Account Compromise: Credentials were obtained and privileged access was established.
Phase 3: Lateral Movement: Attackers pivoted through MDM/Intune into the VPN and broader internal network.
Phase 4: Wiper Deployment: A mass OS reset was pushed to over 200,000 devices and servers.
Phase 5: Exfiltration and Destruction: 50 TB of data was stolen, executives were emailed, and systems were completely wiped.
Individually, some early-stage weaknesses might slip under the radar of automated vulnerability management tools. Combined, they create an effective attack path allowing attackers to move freely through an organization. This is where internal network testing becomes critical. Security teams have to focus on breaking these potential escalation paths before they can be fully navigated.
Breaking the Chain
Defenders have opportunities to break this chain at several distinct points. Incidents like this only succeed when attackers are able to move through multiple stages without being detected or stopped.
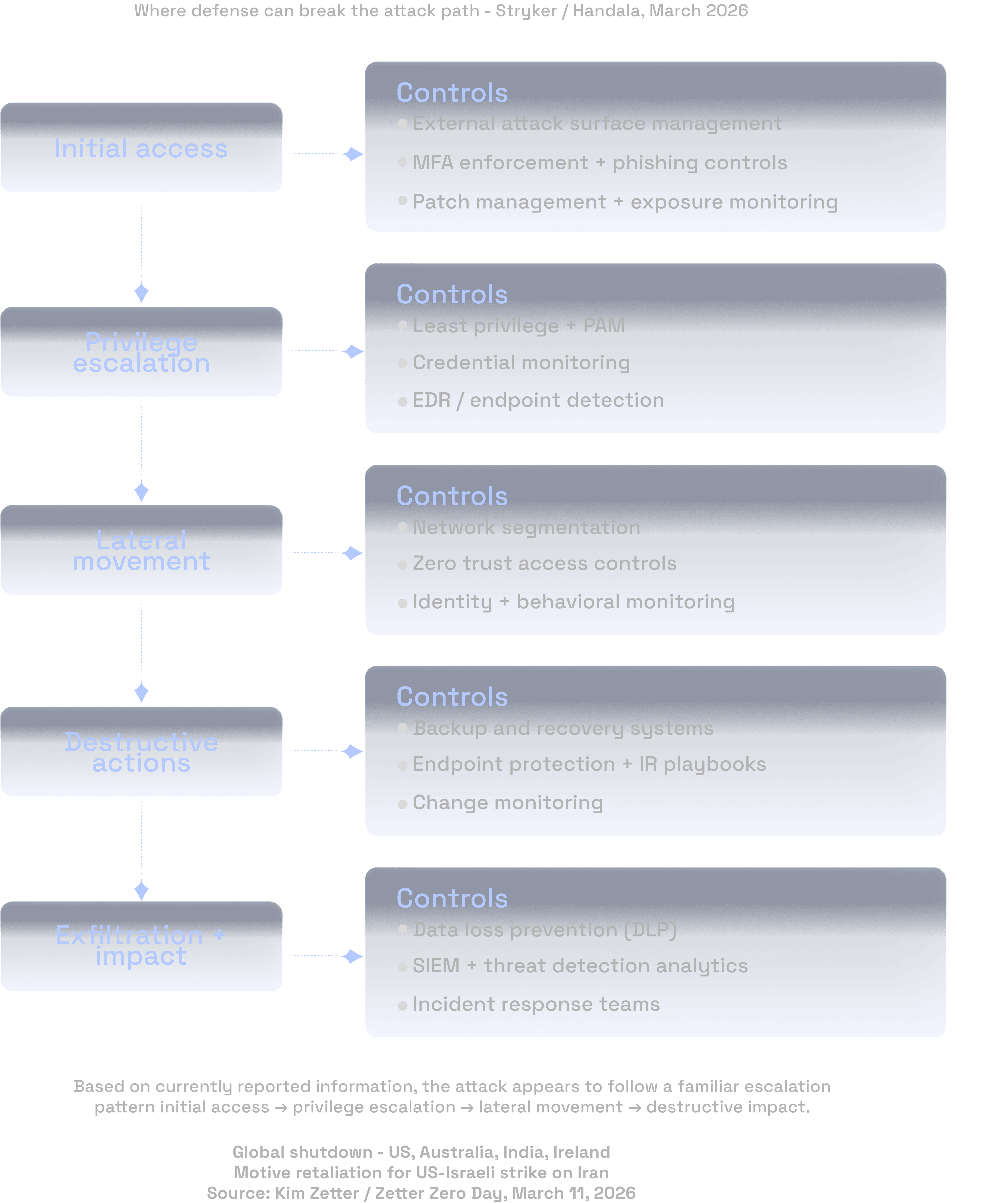
Where defenses can break the attack path. Essential controls mapped to each phase of the Stryker/Handala intrusion
As the diagram above illustrates, stopping an attack requires specific controls mapped to each phase of the intrusion. From enforcing MFA and external attack surface management at the initial access phase to implementing Zero Trust access controls during lateral movement, layering these defenses is what ultimately disrupts the attack path.
The Healthcare Complexity Factor
As a massive medical device manufacturer, Stryker's disruption is sending shockwaves through the healthcare supply chain. Healthcare and medical device environments are uniquely complex to secure.
They often include a volatile mix of clinical systems, connected medical devices, identity platforms, vendor-managed infrastructure, and operational technology.
Many medical devices simply cannot run traditional endpoint protection. Attackers frequently bypass targeting the devices directly, opting to compromise surrounding IT systems instead. They then escalate privileges and move laterally toward the sensitive infrastructure. Understanding how attackers navigate these hybrid environments is essential for cutting off those paths.
The Real Takeaway
Stripping away the hacktivist propaganda reveals a fundamental truth. Identity has effectively become the control plane, and privilege is what determines how far an attacker can go.
When initial access, privilege escalation, and lateral movement happen in the shadows, a small intrusion quickly scales into a major disaster. Strengthening controls around identity and implementing strict privilege management will significantly reduce your risk.
Organizations reviewing the news this week should focus on getting back to basics. Make sure the fundamentals of security, especially around Active Directory, VPN access, and endpoint management tools, are locked down and working exactly as intended.
If you’re unsure how your environment would hold up against this type of attack path, it’s worth validating those assumptions through internal testing.
Anatomy of a Meltdown: What the Handala Attack on Stryker Teaches Us About Privilege Escalation

Anatomy of a Meltdown: What the Handala Attack on Stryker Teaches Us About Privilege Escalation
Mar 18, 2026
Mike Shelton, Head of Pentesting